By now you must have heard of Unit 61398 of the People’s Liberation Army: “an overwhelming percentage of the attacks on American corporations, organizations and government agencies originate in and around [their] white tower,” claims the New York Times, who were themselves recently owned by the 1337 h4ck3r5 of the 61398. And just recently, there were “extremely sophisticated” attacks on Apple, Facebook, and Twitter! Why, those evil Chinese! We can’t just stand by while this happens! The US government has to —
to —
…wait just a minute here.
I don’t know how the NYT defines “overwhelming,” but those Apple/Facebook/Twitter hacks? Those apparently originated in Eastern Europe, a long, long way away from Shanghai. And Chinese hacking? Old, old news. Why, the NYT reported on it — courtesy of Wikileaks — back in 2010:
For example, in 2008 Chinese intruders based in Shanghai and linked to the People’s Liberation Army used a computer document labeled “salary increase — survey and forecast” as bait as part of the sophisticated intrusion scheme that yielded more than 50 megabytes of e-mails and a complete list of user names and passwords from a United States government agency that was not identified.
“Sophisticated.” A word that gets thrown around a lot in reference to these attacks, without much in the way of substantiation. Reports indicate, however, that most of them begin with a so-called ‘spear-phishing’ attack, wherein a hackee is tricked into clicking on a malware-ridden link in an email. “The e-mail, in perfect English,” marvels the NYT, “discussed security weaknesses in critical infrastructure systems, and asked the employee to click a link to a document for more information.”
Full points to the Chinese for spear-phishing with an email about security weaknesses. That’s irony worthy of a crack team of Brits turned Mission hipsters.
It’s true that the Internet would be a lot safer if people’s work machines weren’t typically riddled with bug-ridden bloatware like Flash or (client-side) Java. Believe it or not, software does not have to be a frothy Swiss Cheese of security holes, and we should all uninstall that which is. Instead we seem to have collectively descended into a kind of learned helplessness when it comes to malware.
(Consider, for instance, the Silk Road, a web site that sells drugs and other highly illegal goods online–and yet, despite intense interest from law enforcement, has continued to operate unmolested for years now. They don’t have anything like the resources of a government; they just understand security.)
Google’s doing its best to make the world a safer place. As are security startups like Cryptocat and YC alumnus Cryptoseal–the latter co-founded by one Ryan Lackey, whose colorful war-zone exploits I’ve chronicled before.
But we still need to be fairly worried. As everything-and-I-mean-everything gets networked and automated, hackers grow ever more dangerous. (I wrote a whole novel about this eight years ago.) So what’s a poor antediluvian behemoth of a government to do?
Not what they did, which was bring back CISPA. Sigh. As the EFF put it: “CISPA essentially equates greater cybersecurity with greater surveillance and information sharing. But many of our cybersecurity problems arise from software vulnerabilities and human failings … the types of issues that CISPA doesn’t deal with.”
More generally, security solutions that actually work tend to be bottom-up, not top-down; government attempts to increase its control over the Internet have historically led to worse security. Consider the Chinese hack of Gmail in 2011, when “In order to comply with government search warrants on user data, Google created a backdoor access system into Gmail accounts. This feature is what the Chinese hackers exploited to gain access,” to quote security guru Bruce Schneier, who says of the latest China hacks:
Wow, is this a crazy media frenzy. We should know better. These attacks happen all the time, and just because the media is reporting about them with greater frequency doesn’t mean that they’re happening with greater frequency. […] This is not cyberwar.
Indeed. So disable Java, turn off Flash, and don’t click on attachments (especially PDFs) unless you’re sure they were sent in good faith–but don’t lose too much sleep over PLA Unit 61398, and put no faith in heightened government control over the Internet. That would probably only make things easier for all the world’s “highly sophisticated” hackers, whether they hail from China, Eastern Europe or right next door.
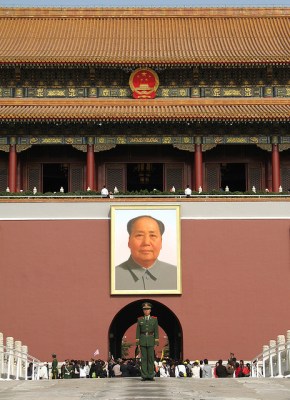
Image credit: Tiananmen Square, by yours truly.