ENISA, the European Network and Information Security Agency, today named drive-by exploits as the biggest, most increasing threat of the moment in the Internet landscape, amongst a sea of other all-too-familiar issues like worms, phishing and botnets. Spam, one of the oldest and most annoying aspects of being online, is the only threat that is on the wane, according to ENISA’s Threat Landscape report out today.
In a year that saw DDoS attacks from Anonymous (or those claiming to be with the group), defacements of high-profile websites, and many other security breaches, ENISA’s extensive report goes through the most common and most dangerous tactics used by malicious hackers to worm their way into your data, giving examples of how they have been used, and some suggestions for how to deal with them. Other threats that made the top ten include worms, Trojans, code injection, exploit kits, botnets, denial of service attacks, phishing, compromising confidential information, rogueware/scareware, targeted attacks, physical theft/loss/damage, identity theft, abuse of information, search engine poisoning and rogue certificates.
And given that a lot of the threats are global, with attacks coming from everywhere and aimed at everything, a European report has just as many ramifications for people outside the region as inside it.
Drive-by exploits, as background, are when someone has injected malicious code into the HTML code of a website. That code in turn affects users’ browsers, plug-ins and operating systems when they visit the site, and can be used to then glean other information. The sites themselves may be unknowingly hosting the malicious code.
By nature, these are stealthy vulnerabilities, but occasionally high-profile instances of them come to light. Drive-by exploits is something that Google points out can be a reason for why it chooses occasionally to block certain sites through its browser and searches. This is something that appears to have come up the other week, when Google suddenly started blocking Twitpic and pages that pointed to it. Google never commented on the situation, but sources close to the matter tell me that the warning was not in error, and not a false positive as some guessed. Given that Twitpic was surprised by Google’s block the other week, a drive-by vulnerability, unbeknownst to Twitpic, could may well have been the reason behind it.
It’s not just websites that are feeling the effects of drive-by exploits.
ENISA notes that the first drive-by for Android was discovered in May 2012, and that in fact mobile platforms (led by Android) are one of the biggest targets for these. Between mobile, social technology, critical infrastructure, trust infrastructure, cloud and big data, ENISA says that trust infrastructure — “any information system that provides strong authentication and aims at establishing a trusted, secure connection between two end points” — is the only one not threatened by drive-by exploits. That would make sense since that is the only one of the group that does not involve public internet usage of any kind.
Below is Enisa’s full list top ten emerging threats, and how they are faring across all the different mediums. Under that, I’ve included a closer look at threats for mobile in particular, since it is the fastest-growing, most dynamic, and possibly least understood/controlled of all of these different areas at the moment.
Separately, all of these issues were also highlighted today Deloitte‘s 2013 TMT Security Survey, released today. Looking at data security issues among enterprises, it found that the top three vulnerabilities, as seen by the end users themselves, were the number of third-parties they need to deal with online (78% saw this as the biggest vulnerability); the use of mobile devices (74%) and a lack of awareness about security vulnerabilities and correct procedure by employees (70%).
The full ENISA report is an eye-watering 96 pages long and has the details for all the other categories. It’s embedded below, and is a great reference in that it provides extensive examples of how each of these threats has been appearing and developing over the last year. The report also offers some guidelines for how organizations and individuals can best tackle the threats. Update: I’ve also added in the Deloitte report now, too.
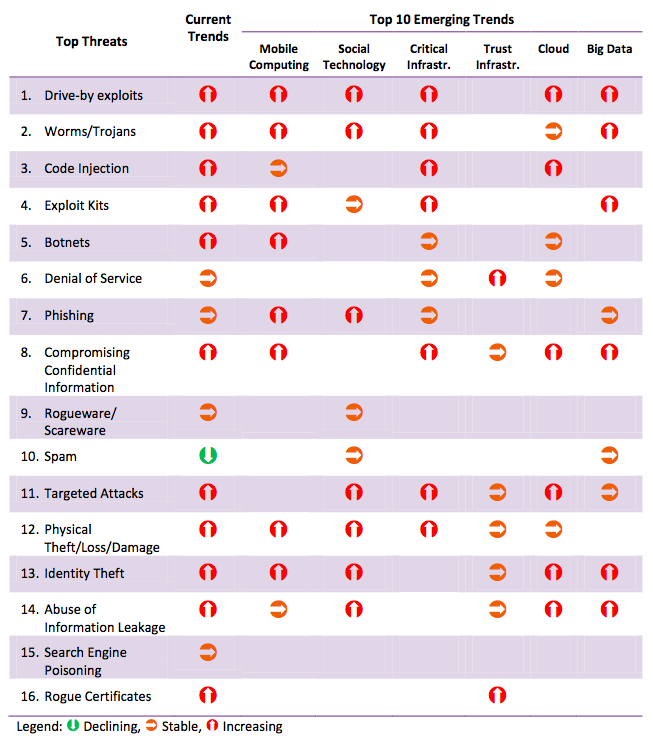
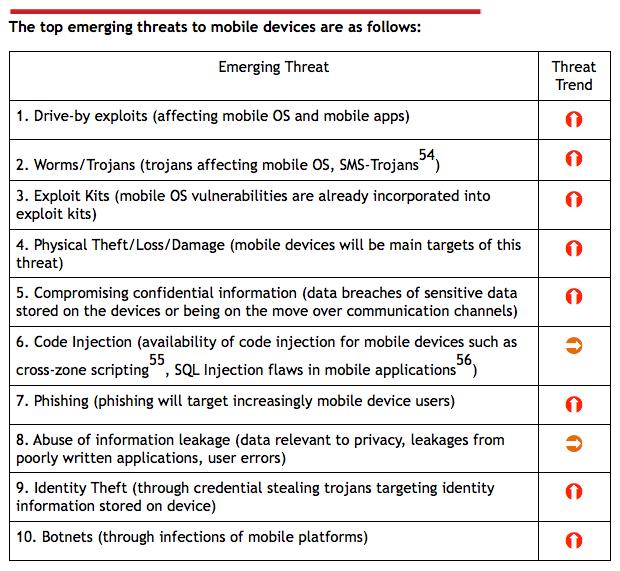
Image: Flickr
