Online payment company Stripe launched a very cool online contest today that plays off the computer security world’s well-known war game: Capture the Flag.
In Stripe’s version, app developers discover and try to exploit vulnerabilities in mock web apps. The contest launched at noon today and in the first six hours 4,500 people signed up. The contest will be live for a week. After that, the company plans to release the source code so people can analyze or run it themselves.
Now this is what the security space needs — a way to get developers into something that is fun but also helps them learn about how to make their web apps more secure.
Stripe’s focus is on making it easy for developers to accept credit cards. So it makes sense that the company has an interest in helping developers strengthen their security skills.
CEO Patrick Collison said in an email interview today that major breaches are increasingly common. Yahoo!, Dropbox and LinkedIn are just a few that have had breaches in the past few months.
Collison makes the point that developers know security is important but few get hands on experience needed. Once attacked, it really is too late.
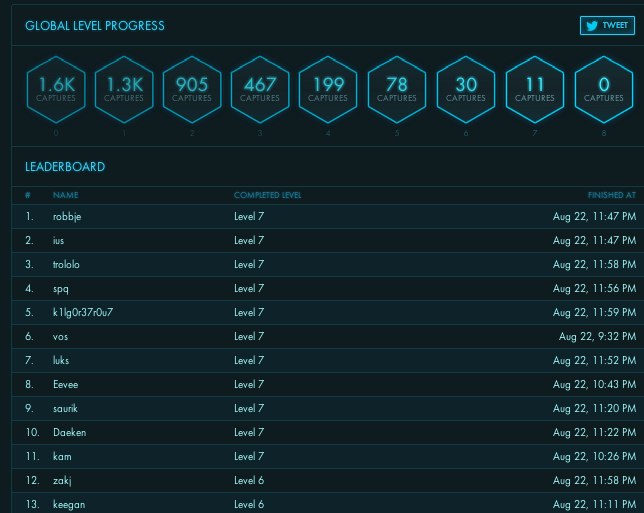
To play, developers sign up at Stripe CTF. Once signed in, you enter the game, which has eight levels. As of writing this post, no one has yet made it through each level. A leaderboard gives the latest results for how people are faring in the game. Winners who complete all levels get a special-edition Stripe Web CTF T-shirt, designed for the contest.
The game helps developers understand how different attacks work. As the Stripe blog points out, ever wonder how a CSRF attack works? The Stripe Capture the Flag contest is the place to learn. By the end of the experience, the hope is that it will help developers write more secure code, have some fun and perhaps be enlightening, too.