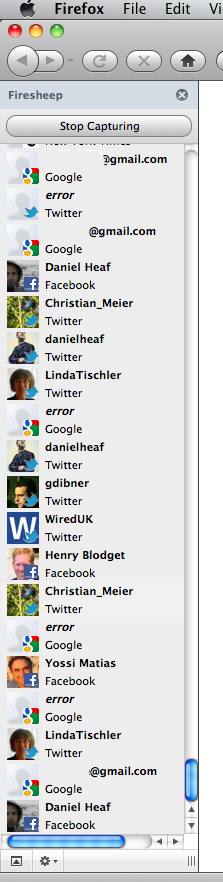
Remember Firesheep, that Firefox extension that lets users effortlessly ‘hack’ into the Twitter and Facebook accounts of anyone using a public network by capturing user cookies?
I’m currently at the DLD Conference in Munich, Germany, which is host to a whole lot of tech luminaries, executives, startups, press and investors alike.
The organization has provided every attendee with access to a public WiFi network dubbed DLDpublic, and lo and behold, looks like many of them haven’t taken any measures to prevent the above-described hijacking from happening.
Sure enough, my TechCrunch colleague Mike Butcher quickly became a victim of my desire to check out how serious a security issue this really is.
For the record: I was one of the people whose accounts could easily be ‘HTTP session hijacked’, and fortunately someone – an unnamed experienced startup’s CTO – brought that to my attention. This person assured me that he ran Firesheep out of interest and boredom, and not with malicious intentions, and that he would love nothing more than to warn everyone about the risks.
I figured I should extend everyone with the same courtesy by posting about it here, as it’s simply not doable to warn hundreds of people individually.
Apparently, logging off these services helps, somewhat.
I also figured it’s a good way to remind all our readers that tools like Firesheep exist, that they’re not the cause, and what you can do to avoid your social network accounts from getting hijacked.
To be absolutely clear, I’ve also contacted the organizers of DLD, and they’re doing all they can to mitigate the issue.
This is obviously not their fault, but they’re taking all precautions they possibly can, and agreed that the right thing to do is publish and warn everybody about the security issue this way.
Next time you’re at an event with an open WiFi network, you might want to consider using a secure VPN to connect to the Internet anyway – you never know who’s sniffing.
That includes you Esther Dyson, (Mozilla CEO) Mitchell Baker, Kai-Fu Lee, Henry Blodget, WiredUK, etcetera.