 I mentioned a newly released hardware encrypted USB flash drive last week, and promised a full review. Here it is! The Lexar JumpDrive SAFE S3000 FIPS is a hardware-encrypted USB drive that satisfies U.S. government computer security standard FIPS 140-2 Level 3. “Physical security mechanisms required at Security Level 3 are intended to have a high probability of detecting and responding to attempts at physical access, use or modification of the cryptographic module.”
I mentioned a newly released hardware encrypted USB flash drive last week, and promised a full review. Here it is! The Lexar JumpDrive SAFE S3000 FIPS is a hardware-encrypted USB drive that satisfies U.S. government computer security standard FIPS 140-2 Level 3. “Physical security mechanisms required at Security Level 3 are intended to have a high probability of detecting and responding to attempts at physical access, use or modification of the cryptographic module.”
The SAFE S3000 FIPS accomplishes this by means of a Gemalto .NET V2.2 FIPS smart card, which provides “tamper-resistant storage, isolation of all security-critical computations, and strong authentication through a stringent PKI-based challenge-response process.”
The metal casing is water proof, and the entire thing is filled with “military-grade epoxy compound” to thwart physical access. This drive has some serious heft to it, compared to other USB sticks. In a pinch, you could probably cause modest pain to someone by throwing it at them. Seriously, this thing is solid.
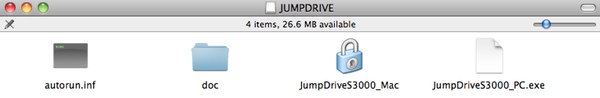
When you plug this into your Windows or Mac computer, you’ll see a small partition that contains a simple helper program to unlock the drive. If you’re a PC, double click the JumpDriveS3000_PC.exe, and if you’re a Mac, double click the JumpDriveS3000_Mac application.
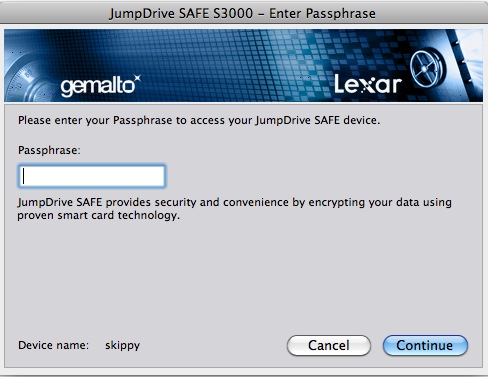
Upon first use, you’ll be walked through the setup process. You assign a passphrase to unlock the device, and an optional security question to use in case you forget the first passphrase. This security question must be selected from a list of pre-defined questions (mother’s maiden name, name of first pet, etc), which somewhat limits the security of this process. More on this below.
Once configured, you’ll be prompted to type your passphrase to unlock the encrypted partition:
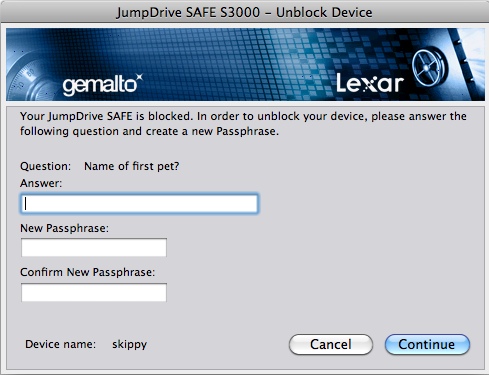
Enter the wrong passphrase too many times and you’ll lock your device. If you provided an optional security question, you can use that to reset a forgotten password:
One unlocked, you get a new USB device attached to your system, named SAFE:

Copy files to this location as needed: everything gets encrypted on the fly. When you’re all done, unmount the drive and remove the USB stick from your computer.
As you can see, once you’ve authenticated to the secured partition, this thing acts like any other USB drive. No problems, no hassles.
The software supplied on the SAFE S3000 is for Windows and Mac only. A Linux machine can see the unencrypted read-only partition just fine, but is unable to access the encrypted partition. Here’s what a Linux system sees when you insert this device:
[1204303.796012] usb 1-8: new high speed USB device using ehci_hcd and address 4 [1204311.357306] usb 1-8: configuration #1 chosen from 1 choice [1204311.357641] scsi7 : SCSI emulation for USB Mass Storage devices [1204311.357825] usb-storage: device found at 4 [1204311.357827] usb-storage: waiting for device to settle before scanning [1204311.372595] input: Lexar JumpDrive SAFE S3000 USB Device as /devices/pci0000:00/0000:00:1d.7/usb1/1-8/1-8:1.1/input/input6 [1204311.393196] generic-usb 0003:05DC:0801.0002: input,hidraw1: USB HID v1.01 Gamepad [Lexar JumpDrive SAFE S3000 USB Device ] on usb-0000:00:1d.7-8/input1 [1204316.356127] usb-storage: device scan complete [1204316.356484] scsi 7:0:0:0: Direct-Access LEXAR JD SAFE S3000 1511 PQ: 0 ANSI: 1 CCS [1204316.357228] scsi 7:0:0:1: Direct-Access LEXAR JD SAFE S3000 1511 PQ: 0 ANSI: 1 CCS [1204316.358722] sd 7:0:0:0: [sdb] 61440 512-byte hardware sectors: (31.4 MB/30.0 MiB) [1204316.360597] sd 7:0:0:0: [sdb] Write Protect is on [1204316.360600] sd 7:0:0:0: [sdb] Mode Sense: 23 00 80 00 [1204316.360603] sd 7:0:0:0: [sdb] Assuming drive cache: write through [1204316.363093] sd 7:0:0:0: [sdb] 61440 512-byte hardware sectors: (31.4 MB/30.0 MiB) [1204316.363589] sd 7:0:0:0: [sdb] Write Protect is on [1204316.363592] sd 7:0:0:0: [sdb] Mode Sense: 23 00 80 00 [1204316.363594] sd 7:0:0:0: [sdb] Assuming drive cache: write through [1204316.363598] sdb: [1204316.366016] sd 7:0:0:0: [sdb] Attached SCSI removable disk [1204316.366479] sd 7:0:0:0: Attached scsi generic sg2 type 0 [1204316.370217] sd 7:0:0:1: [sdc] Attached SCSI removable disk [1204316.370295] sd 7:0:0:1: Attached scsi generic sg3 type 0 [1205369.339282] usb 1-8: USB disconnect, address 4 [2354955.204015] usb 1-8: new high speed USB device using ehci_hcd and address 5
And here’s what happens when I try to access it:
scott@mgr5:~$ sudo mount -t vfat /dev/sdb /mnt mount: block device /dev/sdb is write-protected, mounting read-only scott@mgr5:~$ ls /mnt autorun.inf doc JumpDriveS3000_Mac.app JumpDriveS3000_PC.exe scott@mgr5:~$ sudo umount /mnt scott@mgr5:~$ sudo mount -t vfat /dev/sdc /mnt mount: no medium found on /dev/sdc scott@mgr5:~$ sudo cat /dev/sdc cat: /dev/sdc: No medium found
As you can see, I can access the unencrypted /dev/sdb partition just fine; but am unable to access the encrypted /dev/sdc partition. The helper program contained on the unencrypted program works the necessary magic to make the encrypted partition accessible to the computer.
What happens when you enter the wrong password too many times? This is where the issue of the security question becomes important. The product manual does an absolutely terrible job of describing the situation. If you do not set a security question, then after 5 incorrect password attempts you are prompted to “reset” the drive. This purges all the encrypted data, and starts the initialization process.
If you do set a security question, after 5 failed password attempts you are prompted to input the security question answer in order to reset the password used to unlock the device. If you enter an incorrect security question response five times, your S3000 FIPS is permanently locked.
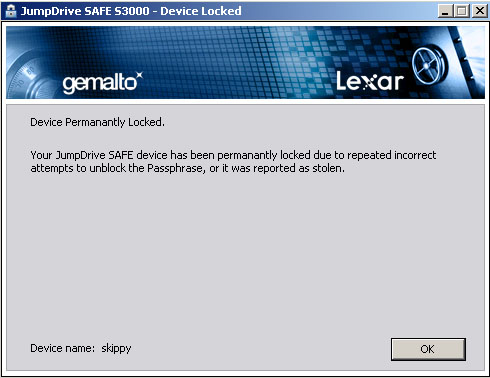
As part of the review process, I intentionally entered the wrong passwords — as would anyone who found one of these drives in a taxi or on a subway — to see how the process worked. I can confirm that I am now the proud owner of a Lexar-branded paperweight. Yay!
I called Lexar to make sure there was no recovery possible. The friendly tech support person I spoke with confirmed that a locked S3000 FIPS is unrecoverable. Jyh Chau, senior product manager with Lexar, provided me with the following response:
By design we enable the owner/end user of the JumpDrive SAFE S3000 FIPS to register a log-in password and a security question and answer (Q&A). The login password is mandatory for accessing the secure storage area.
The security Q&A provides a way for the user to recover from a lost password situation. It is optional but we do recommend users set it up to avoid data loss in a lost password situation.
If the security Q&A is not set, the user has the option to “recycle” the drive. All data will be securely erased, returning the drive to its original state. A new log-in password will need to be registered before the secure storage area can be used.
If the security Q&A is set, the drive is now in a full protect mode. If both log-in and security Q&A attempts are exceeded, the drive will be permanently disabled. In terms of threat model, the design ensures that only the true owner/user is able to use the device after the full protect mode is enabled. In high security computing environments this is a desirable trait (not allowing an unauthorized user to recycle a drive and use it within the environment).
The 8GB model I tested runs $199 direct from Lexar which seems extremely expensive to me. But then again, I’m not dealing with million-dollar research data, so perhaps this is actually a drop in the bucket compared to the cost of losing valuable data.
Bottom Line
If you have government blueprints, or other super-secret data, the JumpDrive SAFE S3000 FIPS is a solid, secure means of transporting that data around. Just don’t forget your password.