As long as advertisers pay for clicks, there will be click fraud. And the more people combat it, the more sophisticated the attacks become to get around the defenses that advertisers, search engines, and others put in place. But a recent click fraud ring discovered by click-fraud monitoring service Anchor Intelligence suggests that the practice is evolving to a scale never seen before.
Anchor Intelligence identified a click fraud ring being run out of China which involved 200,000 different IP addresses and racked up more than $3 million worth of fraudulent clicks across 2,000 advertisers in a two-week period. That money was never paid out and the ring has now dissipated (or moved onto another scam), but who knows how long the ring was in operation before Anchor noticed. The operation was called DormRing1 because it was centered in dorms at technical universities in China such as the Shanghai Technology Institute.
“We have seen 200 fraud rings,” says Anchor VP Richard Sim, “and this one by far trumps them all. I think it is indicative of how sophisticated the click fraud is getting. We are seeing the sheer scale and size of these rings growing.”
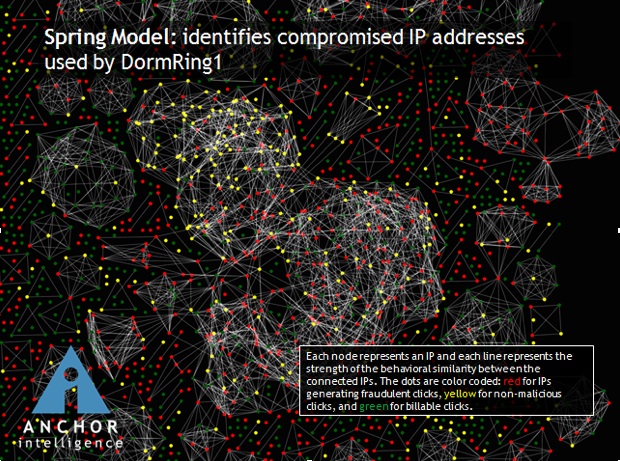
Click fraud occurs when someone sets up a website, signs up with an ad network, and then clicks on the ads to generate ad revenues with false clicks. DormRing1 operated the same way, except it easily involved more than 1,000 people who set up more than 10,000 Websites to spread out the fraud. The image above depicts a portion of the ring, with each red dot representing a source of fraudulent clicks with similar digital signatures. (Anchor monitors such activity on behalf of advertising clients).
Spreading the click fraud out across thousands of sites makes it harder to detect, but it also requires a lot more people to perpetrate it. DormRing1 recruited student click fraud workers on Chinese social networks where and forums participants would post images of checks they were getting for their activities. One drummed up interest by talking about his plans to buy a car with the proceeds. Just like with any criminal organization, people at the lower rungs had to do a lot of grunt work to move up the ladder of trust and money. A briefing paper provided by Anchor describes the operation:
These social networks involve a complex set of user access levels. The baseline entrance level is only available by invitation; access to sensitive information is restricted solely to those users who have attained the highest levels. Users with the uppermost levels of access are able to purchase root kits to engage in fraudulent activity and contract out phases of their fraud operations to a large network of willing participants. Users reach higher levels of access in one of two ways: either through a vouching system or by proving themselves as valuable contributors to the network through the provision of some ground level of services (e.g. contracting to create hundreds of accounts on various websites).
DormRing1 was able to use these exclusive social networks to create a division of labor in which all participants at the highest levels shared in a percentage of profits from an operation. The students involved in the ring each set up dozens of bare-bones websites, and successfully registered them with multiple ad networks. The students then hired the services of several botnet controllers to systematically click on ad links that were displayed on these sites. For each ad click, the publisher made a percentage of what the advertiser paid for that click. Through this network, the perpetrators were able to contract money mules (i.e. people with US addresses to which checks can be sent), traffic generators / botnet herders, website template developers, and a host of other service providers. After monetizing these fake websites via fraudulent ad clicks, the perpetrators then wired money to their various contractors.
Remember, we only know these details because DormRing1 was stopped. But nobody was arrested. The advertisers just stopped making payments to the fraudulent Websites. You can be pretty sure that DormRing2 is already up and running.