In the last 24 hours there has been a sudden surge in the amount of spam being sent and received by MySpace users, suggesting that the site has fallen prey to a security exploit that grants spammers access to accounts. Many users are logging in to find that they’ve commented on their friend’s status updates with spammy messages inviting them to “make $$ this summer”. We’ve reached out to MySpace to ensure that they are aware of the issue.
In the last 24 hours there has been a sudden surge in the amount of spam being sent and received by MySpace users, suggesting that the site has fallen prey to a security exploit that grants spammers access to accounts. Many users are logging in to find that they’ve commented on their friend’s status updates with spammy messages inviting them to “make $$ this summer”. We’ve reached out to MySpace to ensure that they are aware of the issue.
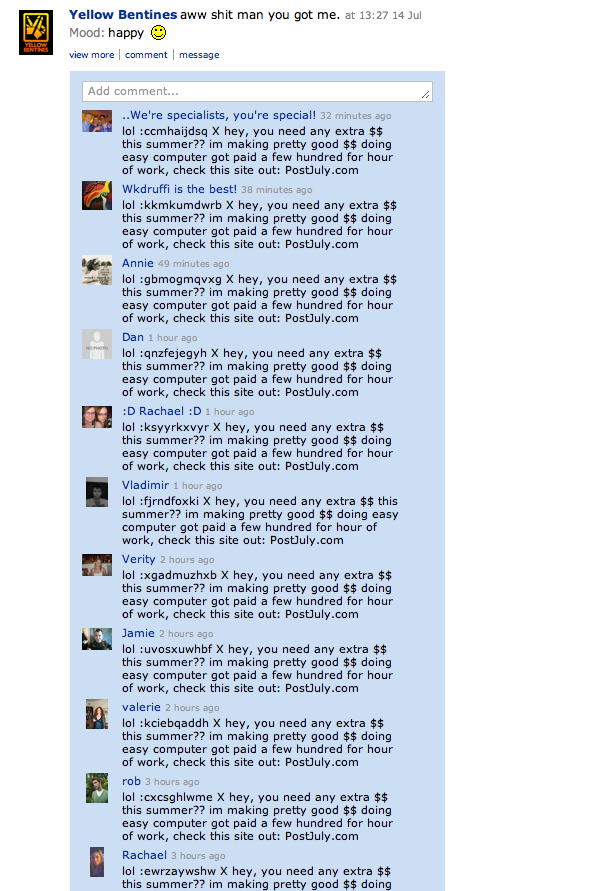
Some MySpacers are speculating on the site’s forums that the hack is tied to phishing links in status updates, which seems to be in line with the reports we’ve seen of literally hundreds of identical spam status updates to certain band profiles (see the screenshot below).
Update: We’ve learned that this is in fact the case — MySpace users are falling prey to a phishing attack through links in status updates that invite them to renter their login information, which is then used to spam their accounts. MySpace expects to have a fix for this out later today that will remove all of these links.
Phishing attacks are notoriously difficult for social networks to defend against, as they rely on tricking users into handing over their account info rather than breaking through a site’s security measures. Facebook has also been hit by a number of similar attacks.
During our interview with Hacker Croll regarding the recent Twitter break-in, he revealed that there is at least one security hole in MySpace that is well known in the hacker/cracker community that grants access to MySpace accounts. Unfortunately he was unwilling to share the exploit, but we warned MySpace about it late last week. It is unclear if this attack is related. The phishing attack is probably unrelated, which likely means there are still outstanding exploits.
This is only the latest in a long string of recent security attacks against major web services. Last week Twitter fell prey to a massive security breach revealing internal documents, while developer-outsourcing site Elance got hit by a hack as well that compromised some user data.
Thanks to Aaron Parker for the tip.