Editor’s note: Adam Kujawa is head of Malware Intelligence for Malwarebytes Labs. He specializes in reverse-engineering, malware research and threat education.
The word “exploit” is harsh. Even ugly. It suggests cynical manipulation, selfish misappropriation and even outright theft. In the online world, an exploit is all of those nasty things and then some. Yet for some reason, many startups and consumers don’t take even the most basic steps to stop their digital assets, and even themselves, from being exploited.
They should. Exploits can wreak havoc on consumers and startups, such as stealing bank account passwords and credit-card numbers, encrypting all the files on a computer and demanding a hefty ransom to get them back, and even accessing documents that have recently been copied on your copy machine, such as passports and tax forms. But there are things every startup and user can do to stop exploits.
How can you avoid being hit by one?
Despite the potential damage and the cunning methods used by cyber criminals via exploits to victimize users and their systems, the bulk of them are actually pretty easy to avoid.
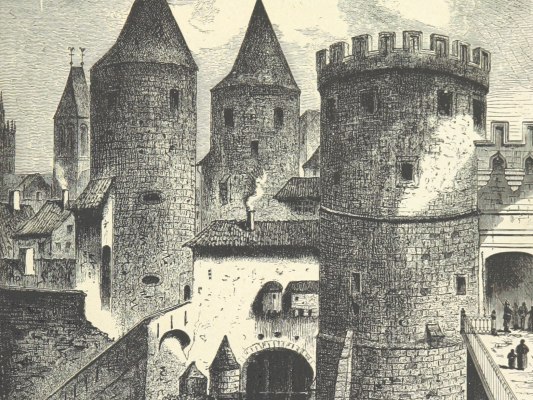
First, since exploits target specific vulnerabilities, this step is easy: Patch vulnerabilities. A computer system can best be thought of as a castle. Like fixing holes in the castle walls, keep commonly attacked software, like Internet Explorer, Adobe Flash and Java, updated at all times. If you do, the chance of being exploited will be dramatically reduced.
The next step is to limit the amount of vulnerable software on your system. This is like boarding up gates that aren’t commonly used — especially the ones that are full of holes. Old software that you no longer use can be a potential target for an exploit attack, so uninstalling them may save you a lot of heartache later. In addition, disabling commonly installed browser extensions like Java are a great way to avoid many common exploit attacks.
Consider using two browsers — one with all the browser extensions and accessories you need to visit your favorite sites (like Java, Flash, etc.), and another without all those bells and whistles for surfing less trusted websites. It’s like installing two gates to the castle; one is used only for the safety-minded, trusted merchants while the other is for everyone else, and it’s made of solid steel and protected by dozens of guards.
Use caution when surfing the Internet. This may seem obvious but it can make a huge difference in whether or not an exploit makes it through. Avoid risky websites and always double-check the sources of emails or files — even when they appear to be sent from a friend.
The What And How of Exploits
Now that you know why you should be concerned about exploits and how to stop them, here’s the nitty gritty on what they are. Thinking again of your computer system as a castle — the walls are built with the operating system and the gates are built with Internet facing applications, like your browser. Vulnerabilities are holes in the gates and walls that can be easily fixed but are often ignored. Exploits can be thought of as traitors to the kingdom that help enemies enter the castle walls – they know about the holes and the best way to ‘exploit’ them.
Stepping back from the castle analogy, the real world form of an exploit is specially designed code that can take advantage of a software vulnerability. The exploit targets the vulnerability and essentially breaks the application, then forces it to execute malicious software or malware.
The most common type of exploit we see today is what is referred to as a ‘drive-by’ exploit, which resides, hidden, on a web page and is executed once the user visits that web page through their browser. Going back to the castle, think of a ‘drive-by’ as an enemy rushing the gate while a train of carts enter the castle walls. They are commonly unexpected and they move quickly.
The ‘drive-by’ method is so effective because it doesn’t always require the user to be involved in dangerous behavior for it to work. Often times the attackers simply hijack a legitimate site with weak security and insert their malicious code. However it is also possible to launch an exploit attack by using a compromised banner advertisement, these ads could potentially attack the user on any website they go to, even the trusted ones.
Another commonly seen exploit is infected documents, usually sent via e-mail to the victim. The attackers utilize a form of phishing attack that turns e-mails into ‘click-bait,’ enticing users to open attachments. In so doing, they unwillingly let their systems be exploited. Like a merchant cart on its way to the castle that has enemies hiding themselves underneath its cargo, users have no idea that their systems have been compromised.
The goal of any exploit is to break into the system and execute malware. The malware can be anything from your run of the mill password stealers and webcam hijackers to more heinous software like ransomware, which encrypts files and locks down systems, demanding payment.
The sad truth is that while you can avoid 90-95 percent of all exploits on the net right now just by using the practices above, there are still situations that dictate additional security. New vulnerabilities are being discovered all the time, and not just for the same old software but also that which has not been exploited before.
To illustrate, rather than the bad guys coming through a holy gate, they may catapult over the walls, dig under them, or just smash right through. To preempt new surprise attacks and ensure greater security, try to protect against the inevitable by employing additional security layers.
One of the more recent developments is the invention of anti-exploit software specifically designed to detect when an exploit is taking place and block it, eliminating its ability to do harm.
Imagine a bad guy wedges through a hole in a gate and as soon as his foot touches the floor he’s hit with a barrage of arrows. Anti-exploit technology is still new but has already shown a great deal of potential; these days, using a free version at minimum should be considered a must.
Finally, using a time-tested method of castle defense is still very applicable today. That’s the use of security software, and newer forms of anti-malware in particular, including free ones. In the event an enemy pushes through a hole in your gate and makes it past the archers, they’ll still have to deal with the army of trained knights keeping an eye on the good people of the kingdom. Most of the time, the malware delivered by exploits never makes it past security.
Knowledge is power
A decade ago, theft and fraud were primarily perpetrated in the physical world we lived in; but today with so much of our lives online, we must be wary and always on guard. The new battleground is online, and criminals will lie, cheat, steal and destroy lives just to make a buck.
Our computer systems are our castles and our files, passwords and applications our citizens; you, the user, are the ruler of a kingdom under siege. This war may never end and the attacks will most certainly get worse, the bad guys smarter, and our defenses more sophisticated. But the key to security, the greatest weapon any castle can have in the fight against cyber-crime, is knowledge.