A quick follow-up to the problem with the bots invading dating app Tinder which are pushing people to download a mobile game called “Castle Clash” using fake profiles and a domain (“Tinderverified.com”) designed to give the scam an air of legitimacy: the company behind the game in question is today claiming they are a victim, too, not the culprit.
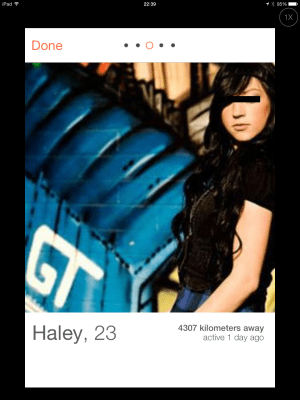
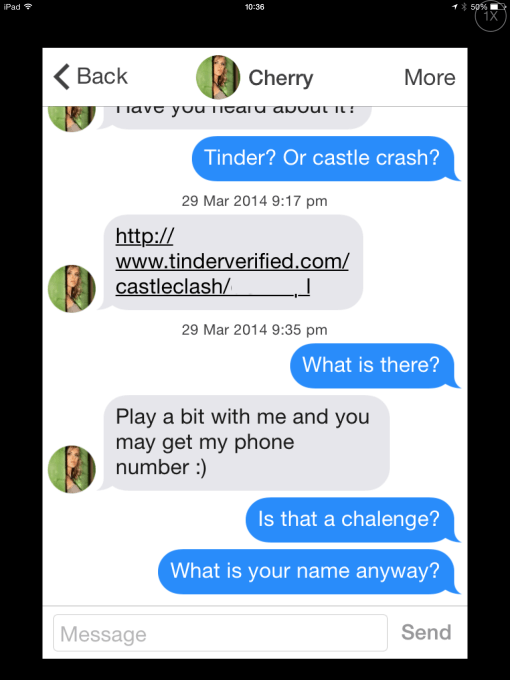
For background, Tinder users are being matched with fake profiles, which are actually just bots, who then proceed to message their matches in the app, linking to the game or other content. Tinder said yesterday it was addressing the problem, which it deemed an “isolated incident.”
 Though the game company behind “Castle Clash,” IGG.com, never responded to our inquires about the matter, they did provide a statement to security firm Bitdefender which is looking into the situation further.
Though the game company behind “Castle Clash,” IGG.com, never responded to our inquires about the matter, they did provide a statement to security firm Bitdefender which is looking into the situation further.
“We are already aware of the issue and we are currently investigating into it. We are also being victimized in this issue therefore we are grateful for being informed,” said IGG’s Jiayan Wu, in response to Bitdefender’s outreach.
We had theorized that it was possible that the developer was a victim of an unscrupulous pay-per-install scheme, where they had contracted with a firm to boost their game’s downloads, and it was that third-party who had actually come up with this ingenious exploit. It may be hard to prove that’s the case, however.
Bitdefender was also able to determine a bit more about this ongoing scam, including the fact that the scam appears to be geo-specific, meaning Tinder’s U.S. users are sent to the “Castle Clash” download while U.K. users and others may be pointed to other fraudulent content, including “surveys and dubious links” for ASDA and Tesco vouchers, the firm says.
The company was also able to pinpoint and notify the Arizona-based photography studio where the bots’ pictures were stolen from, which were also being used for fake Facebook profiles. More to come.