The CrunchGov Essential is a scannable roundup of technology’s influence on the day’s big issues. Below a feature post, we present the most thoughtful, outrageous, and inspiring stories told through the web’s best content. Sign up for the morning newsletter here.
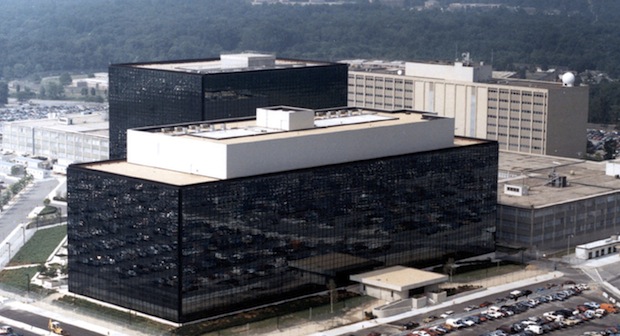
While the world parses the ramifications of the National Security Agency’s massive snooping operation, it’s important to remember an earlier government attempt at data collection and, more important, how a group of hackers and activists banded together to stop it.
In the early 1990s, the military was petrified that encryption technologies would leave them blind to the growing use of mobile and digital communications, so they hatched a plan to ban to place a hardware patch that gave the NSA backdoor wiretap access, the so-called “Clipper Chip“.
After hearing about the plan, a grassroots cabal of hackers, engineers, and academics erupted in protest, sparking a nationwide campaign to discredit the security and business implications of the Clipper chip, ultimately bringing the NSA’s plans to a screeching halt.
Now, the anti-authority community of programmers and tech execs are gearing up for another fight against the NSA’s top-secret Internet Snooping apparatus, PRISM, and there are some important lessons they could learn from their victorious predecessors.
A Clash Of Tech And Culture

The MYK-78, a.k.a “Clipper Chip”
Intelligence agencies were as eager to monitor the digital schemings of terrorists during the days of Full House as they are today. Worried that the U.S.’ brilliant academic minds would inadvertently arm its enemies with cutting edge encryption, it banned the export of any technologies that could conceal communication.
“If you simply took this technology and released it widely, you were also potentially creating an opportunity for very small terrorist groups, criminals and the like to use this technology to get a kind of perfect information security,” recalls former NSA Attorney General, Stewart Baker.
So, encryption programs on the early Internet browsers were officially treated like a munition, like a missile rocket or sniper scope. This is why you often saw mentions of nuclear weaponry in terms of service for programs using cryptography.
The ban wasn’t sustainable because a quickly growing segment of shopaholics wanted the ability to safely buy Captain Planet t-shirts through the World Wide Web, so the NSA knew it couldn’t hold back the entirety of secure e-commerce for national security purposes. As a first step in allowing technology exports, the Clinton White House lobbied for a pencil-eraser-size hardware patch that would, at the very least, allow intelligence agencies the ability to extend their cherished practice of wiretapping to Zack Morris-style cellular telephones.
Ultimately, the plan was defeated by the very same contingent of technologists and businesses that are fighting the NSA’s PRISM program. “Every technology has with it a predominant ideology part of the culture,” says Baker. “There is a predominant ideology that is handed down from professor to student that says, you know, ‘we have to lean against abuses of this technology to make the state stronger’…people will write code that maximizes individual autonomy and reduces the authority of the government.”
Baker recalls how a coordinated ideological effort, with alternative encryption software, academic attacks on Clipper’s vulnerabilities, and big business lobbying took town the NSAs plan.
Money Talks
“A subculture clash became a battle between Microsoft at the height of its powers and a national security establishment,” recalls Baker, who argues that the need to export products, especially for e-commerce, compelled the business community to win over members of Congress.
Ray Ozzie, Microsoft’s former Chief Software Architect, testified before Congress, and let vulnerable members know that encryption regulations could have cost them between $6 and 9 billion in lost annual revenue. It worked.
“The Government should not be in the business of mandating particular technologies,” said career Senator, Patrick Leahy (still in office).
“They go to the White House, they go to congress, and they explain how it’s going to hurt their business,” adds Steven Levy, who wrote the book on the Clipper Chip wars, Crypto.
Even more than in the ’90’s, the technology industry has close friends in government. The Bay Area fundraised more for Obama than either Hollywood (LA) or Wall Street (New York). Silicon Valley’s massive DC presence is paying off: Google’s intensive lobbying of the Federal Trade Commission’s monopoly charges got their potential multi-million dollar fine reduced to a stern warning.
Already we’re seeing Google’s request to disclose more data on NSA spying practices pay off: the Obama administration has indicated that it may loosen the gag order over which details it can publicize. The industry is just beginning to fight, but Silicon Valley paid big bucks during the campaigns and they have favors waiting to be called in.
The First Amendment Is Your Friend
Lobbying alone didn’t topple the Clipper Chip and export controls. Three months before the White House caved into the tech industry, the Ninth Circuit of appeals struck down export controls on First Amendment grounds.
“Government efforts to control encryption thus may well implicate not only the First Amendment rights of cryptographers intent on pushing the boundaries of their science, but also the constitutional rights of each of us as potential recipients of encryption bounty,” explained the landmark Bernstein vs. US Department of Justice decision.
Though the government officially appealed the ruling, it knew it had a weakened position. “Then the government came to us and said, ‘We want to settle the case’.,” says John Gilmore, founder of the Electronic Frontier Foundation.
Today, the issue of government phone and internet snooping is largely a First Amendment issue. The NSA has gagged both senators and tech companies alike from talking about the program.
There is fierce disagreement over whether email spying has produced results. While the NSA claims that it helped stop the 2009 New York City subway bombing plot, public documents indicate that law enforcement got their best tip from documents in a hard drive, recovered by police in the course of normal investigations.
Google has filed a First Amendment complaint with the Attorney General and Senator Leahy has proposed legislation to disclose more info to members of congress (yes, intelligence info is even hidden from Congress).
So, when tech companies and civil liberty groups sue the government, know that they have a history of winning.
Build Tools Like the Dickens
The nail in the coffin for Clipper was the discovery of its inescapable vulnerabilities. Renowned hacker and Bell Labs engineer, Matt Blaze, “uncovered a flaw in Clipper that would allow a user to bypass the security function of the chip,” wrote Levy, back in 1994. Clipper wasn’t just a backdoor for the government, but any hacker who took over its weak security wall.
On the offense, super-programmers were building free, open source encryption tools, such as Philip Zimmerman’s “Pretty Good Privacy,” which allowed better public oversight of their vulnerabilities and weren’t subject to export regulations. In other words, the government couldn’t stop the grassroots hacker community from spreading the very technology that it aimed to stop.
Today, tools for subverting the NSA have had limited appeal. There’s TOR for secure Internet browsing, and Redphone for secure calling, but they either require everyone to be using the same software or have complex implementations.
“Cryptography isn’t easy and the concepts behind it are not easy to understand. Generally, hiding the complexity of the problem only puts the user at greater risk,” says the TOR project’s Andrew Lewman.
So, while citizens have tech companies and civil rights organizations on their side, the 4th Amendment needs a good user-interface designer.
A Winnable Fight
If history tells us anything, the fight against NSA secrecy is a winnable. Intelligence leaders are ruled by elected officials, military practices are still susceptible to the courts, and hackers can create tools to mask users from broad Internet snooping. Every citizen, whether they vote, support a civil liberties organization, and builds encryption tools, has a role to play.
As John Gilmore reminds me, “the one advantage we have over the NSA is that there are a lot more of us than there are of them.”
For more stories, sign up for the CrunchGov email newsletter here and follow Gregory Ferenstein on Twitter
The Book: 4 Items — Google Suing The IRS, Military Blocks The Guardian, Immigration Reform Passes The Senate, The Daily Show On Texas Computer Fraud
Google Suing The IRS For 83 Billion [CNET]
- Google claims the IRS disallowed a tax break in 2004, which is now worth a hefty $83.5 billion.
- “Google argues that the IRS erroneously disallowed a $238.6 million deduction the company took related to the difference in value between AOL paying to exercise a Google stock warrant and the actual value of the company’s shares.”
- “According to the suit, AOL acquired the $238.6 million in shares about three months before Google priced its IPO and went public. That effectively left Google without those shares to sell in its IPO, and since the warrants were used as remuneration for services AOL was providing to Google at the time, the company wanted to expense the total share outlay.”
- Google is a notorious tax haven shark, skirting billions a year through offshore accounts. So, this suit is, needless to say, ballsy.
Military Blocks The Guardian [Monterey Herald]
- The Military has blocked access to The Guardian Newspaper, in order to protect soldiers from reading leaked classified documents about the NSA.
- Army Spox: “We make every effort to balance the need to preserve information access with operational security… however, there are strict policies and directives in place regarding protecting and handling classified information.”
- It’s a good thing that no one else has written about what The Guardian discovered, so the military’s plan is air-tight. Reminder, these people are in charge of nuclear weapons.
Immigration Reform Has Uphill Battle In The House [TechCrunch]
- The Senate passed a sweeping comprehensive immigration bill yesterday in a 68-32 vote.
- But, Republicans call the bill a “pipe dream,” and plan on passing their own version, currently composed of many different bills, including a separate bill for high-skilled immigrants.
The Daily Show On Texas GOP Computer Fraud
After Wendy Davis’s marathon late-night filibuster of a Texas proposal to limit abortion rights, Republicans attempted to change the electronic timestamps on their votes in support of the bill. Davis’s filibuster had effectively stopped the bill, so the GOP hoped it could retroactively give itself more votes the day before by changing computer records. The Daily Show thought this was brilliant: