He stole Facebook’s source code, but never copied, published, or sold it. Then he was arrested and imprisoned. Now released after four months in jail, Glenn Steven Mangham claims in a blog post that he’s an innocent white hat hacker who was trying to help Facebook patch security vulnerabilities.
However, Facebook responded to my request for a statement about the 26-year old’s claims with “Mr. Mangham’s excuses have already been evaluated and rejected by a court of law, resulting in his conviction and jail time.”
Mangham says he planned to inform Facebook of the vulnerabilities, and could have entered Facebook’s White Hat program that offers security researchers protection against legal repercussions. However, Mangham was arrest after possessing the source code for three weeks without informing Facebook. Is he telling the truth, or lying through his teeth?
 Here’s how the hack went down. Starting April 27th, 2011 from his bedroom in his parents house in Acomb, York, England, Mangham spent two weeks hacking into Facebook using a variety of software. Through Facebook’s old Programming Challenge site where potential hires can try solving puzzles, Mangham hacked in and gained access to Facebook employee Stefan Parker’s account. He used the staff member’s privileges to access internal servers. There he discovered the site’s source code and downloaded it from America back to the U.K.
Here’s how the hack went down. Starting April 27th, 2011 from his bedroom in his parents house in Acomb, York, England, Mangham spent two weeks hacking into Facebook using a variety of software. Through Facebook’s old Programming Challenge site where potential hires can try solving puzzles, Mangham hacked in and gained access to Facebook employee Stefan Parker’s account. He used the staff member’s privileges to access internal servers. There he discovered the site’s source code and downloaded it from America back to the U.K.
Spooked by signs that Facebook was on to him, he claims he was scared to disclose his intrusion to Facebook. Facebook’s White Hat Responsible Disclosure Policy reads,
“If you believe you’ve found a security vulnerability on Facebook, we encourage you to let us know right away. If you give us a reasonable time to respond to your report before making any information public and make a good faith effort to avoid privacy violations, destruction of data and interruption or degradation of our service during your research, we will not bring any lawsuit against you or ask law enforcement to investigate you.”
Three weeks after nabbing the code, the FBI and British law enforcement arrested him in an investigation Facebook said cost it $200,000. Mangham says he’s suspicious of such a high cost, noting “I cannot understand how it took 3 weeks and $200,000 dollars to look in the Apache access log, get my IP address, perform some sense checking and request the record from my Internet Service Provider.”
After two months in prison and after all his computer equipment was destroyed, Mangham was released on bail on the condition he not access the Internet or possess any devices that could, and that he live at home. Then in February 2012 he was sentenced to eight months in prison on three counts of unauthorized access to computer material and unauthorized modification of computer data. A successful appeal a few weeks ago halved his sentence and allowed him to be electronically tagged and released after serving just two more months.
In his tell-all blog post and video, Mangham raises several complaints about how he was treated and offers explanations for his actions, including that:
- The source code was stolen so he could perform more in-depth “white box” security testing on it.
- Precautions were taken to prevent damaging Facebook by writing code to prevent his extraction script from “falling into infinitely recurrent sub-structures” and to slow the speed of requests to avoid throttling Facebook’s servers and “impeding its availability”.
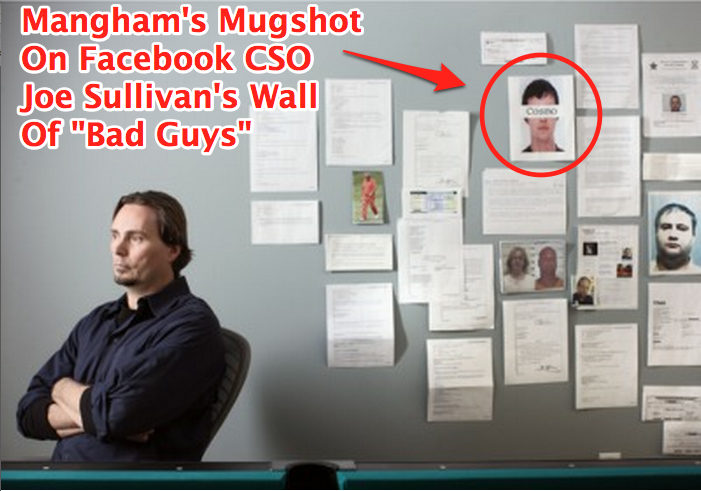
- He claims he was mischaracterized and publicly attacked by Facebook’s Chief Security Officer Joe Sullivan for being malicious when there was no evidence to support that.
- He didn’t immediately report the hole in Facebook’s “outer shell” as he didn’t want it patched before he could catalogue and disclose deeper vulnerabilities.
- He says he didn’t use Facebook’s Bug Bounty system to disclose the flaws because it didn’t exist yet. However, Facebook did maintain ways to report vulnerabilities at the time, though it didn’t yet offer rewards.
- He believes the sentencing was overly harsh despite being thankful that his appeal was granted, especially considering he we never told how exactly his actions cost Facebook so much money.
The most spiteful of his statements attacks Mark Zuckerberg, who himself hacked Harvard’s networks to collect student ID images for use in his “Facemash” predecessor to Facebook. Mangham chides the CEO for employing cybercops like Joe Sullivan that he thinks disregard “The Hacker Way“:
“I’ll tell you what I think is insulting, a company that prides itself on following “The Hacker Way” allowing it’s corporate attack dog to savage someone who did no worse than some of the company’s own founders. It’s not surprising that being a multi-billionaire attracts this dead-eyed breed of soulless sycophant but it would be unwise to believe that they really subscribe to the company philosophy; in another life their jaws would have been firmly clasped around the jugulars of those that they now call their masters.”
In reality, it’s hard to tell whether this is all an elaborate lie designed to clear his name, or whether Mangham actually sought to help Facebook. Statements like the one above certainly don’t paint him as a saint. While he’d been paid by Yahoo in the past for his help, that’s no guarantee of innocence here, and Mangham had his chance at amnesty. Facebook refused to tell me it had proof of Mangham’s malicious intent, but its statement seems to say that Mangham broke the law without disclosing his actions, and that was bad enough.
Still, Facebook is progressive enough to offers $500+ rewards for white hats, and even recently hired one who submitted flaws as an intern. If it wants to maintain its relationship with the hacker community though, Perhaps its disclosure policy could use stronger language than “we encourage you to let us know right away”, such as “we require you”. It begs the question of exactly how soon must white hats disclose their intrusions. Should they be pre-approved?
In the end, delaying disclosure of the vulnerabilities in a quest to find glory in even bigger flaws was stupid and incriminating. White hats and the programs that offer them amnesty are good for the Internet. But if you swim in such dangerous waters without protection, don’t be surprised when the sharks bite.