Jeroen Domburg, aka “sprite”, has written an excellent step-by-step security analysis of the iStorage DiskGenie. The DiskGenie is a hardware encryption solution for portable hard drives that operates completely free of client-side software. The hard drive inside the DiskGenie is unlocked by way of a keypad built into the casing. I’m always a little skeptical of the real-world security of consumer encryption products like this: if there’s one thing I’ve learned over the years it’s that physical access to a device means almost complete control over that device. Domburg delves into some nitty-gritty hardware attacks in his evaluation of the DiskGenie, further reinforcing that physical access is usually complete access.
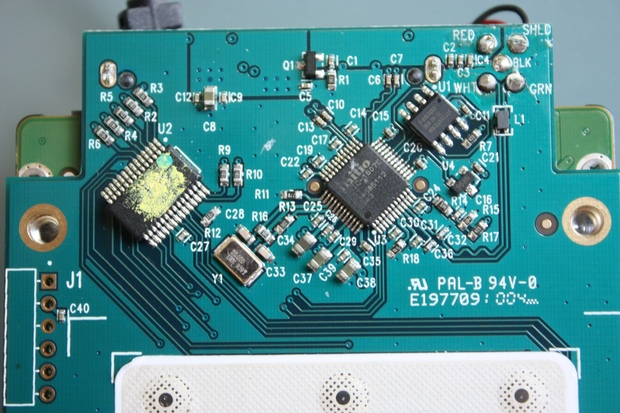
Domburg’s plain-language description of his methodology is great. He succinctly explains the how and why of timing attacks. He looks for ways around the DiskGenie’s bruteforce-prevention mechanisms — even going so far as to create custom circuits to interrupt the internal communications of the device.
Domburg had only relative success with his attacks: he was never able to decrypt the hard drive, but he was able to glean an awful lot of information about the device and how it works. This is one dude, working on his own, with commodity equipment. Just think what a dedicated, professional team could do. As Dimburg summarizes:
So, is it safe? The answer to the question would be (as usual): It depends.
If you’re just a generic Joe Blow who wants to make sure your private pictures don’t get viewed by your collegues or kids, you’re golden. The fact that the there’s no way a software-only attack can get the pincode means that some hardware-experience is needed to start hacking the device, and that will deter casual onlookers enough to make the device completely safe for curious neighbours or collegues, even if they are smart enough to, for example, install a keylogger on your PC.
If you’re a business-person with actual info to hide, info that could financially benefit other parties… you can still use this, but make sure to pick a strong pincode. More than 11 digits should do, depending on how badly others want the data.
Even though I’ve given away the ending, I still highly recommending reading the whole analysis. It’s that good.